Locky ransomware is now spreading via JavaScript (.js) attachments/executable files, which are attached to email messages in .zip files. The following are examples of messages you may receive (click images to enlarge):
When the .js file is clicked, Locky will begin to install and encrypt files with certain file extensions, including unmapped network shares. It will also rename encrypted files to random names with .locky extensions. Ransom notes will appear in the folders of encrypted files, and a ransom note image will appear on the user’s desktop. Other know variants of Locky use the following file types: .doc, .docm and .xls. The ransom message will ask for bitcoin payment in exchange for the encryption key.
If you see .locky extension files appearing on your computer, USB drives, or network shares, please contact the NYU IT Service Desk immediately at 212.998.3333, or at AskIT@nyu.edu, and disconnect your computer from the network. To recover from this infection, we recommend that you restore back-ups from external hard-drives or USB devices. You must wipe the hard drive of an infected machine before mounting back-up devices. It is recommended that you check any files synched with services such as NYU Box, DropBox or Google Drive to ensure these files have not been infected.
If you are not expecting to receive an attachment, do not open it, reply to the message, or click any embedded links in the message. You may opt to verify the authenticity of any email and attachment(s) received by contacting the sender. Suspected phishing attempts may be reported to security@nyu.edu.
For more information, please see:
https://wp.nyu.edu/itsecurity/2016/02/19/locky-ransomware-alert/

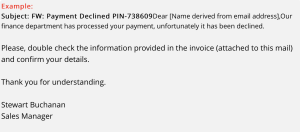
![Screenshot of email message with subject "Payment ACCEPTED M-362827" and text stating "Dear [Name taken from email address] Please check the payment confirmation attached to this email. The transaction should appear on your bank in 2 days.", signed Thank you, Stanley Frank, Financial Manager.](https://bpb-us-e1.wpmucdn.com/wp.nyu.edu/dist/5/2398/files/2016/03/Screen-Shot-2016-03-28-at-12.05.06-PM-300x123.png)